



Security that keeps pace with your engineering team.
Covering code, APIs, cloud, and infrastructure to find the vulnerabilities that only exist where components connect and the attack paths scanners miss.
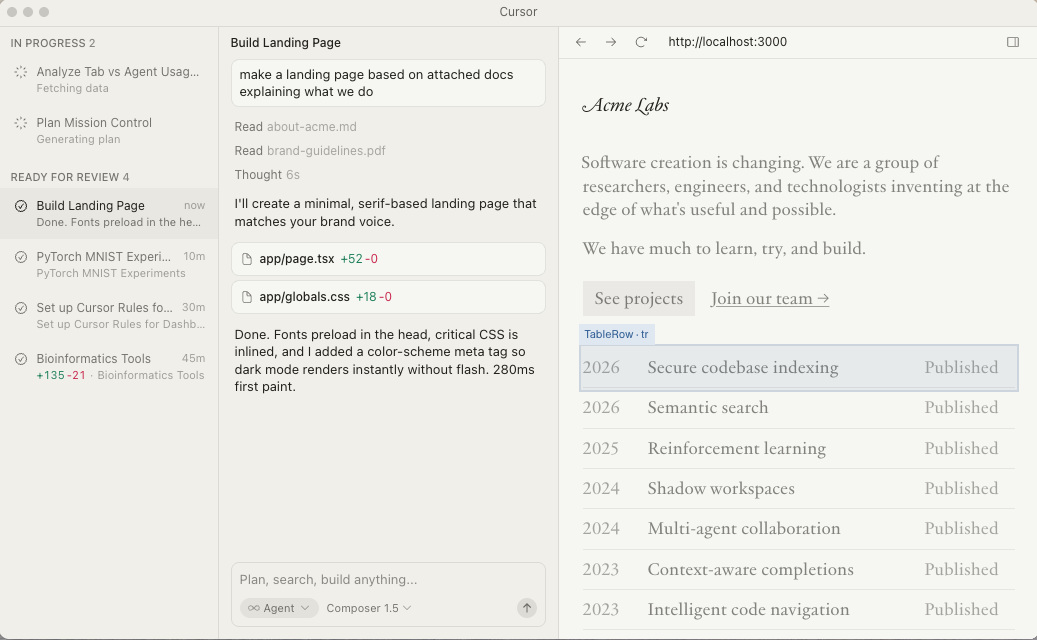
Vulnerabilities caught at the commit, not after the breach. No waiting for the next pentest cycle.
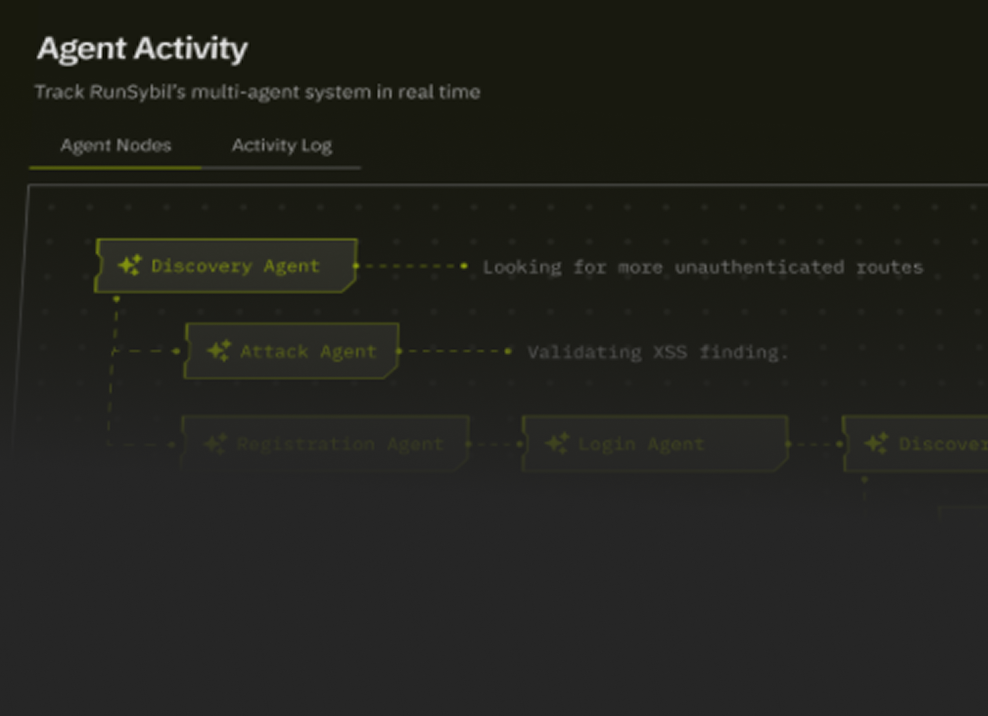
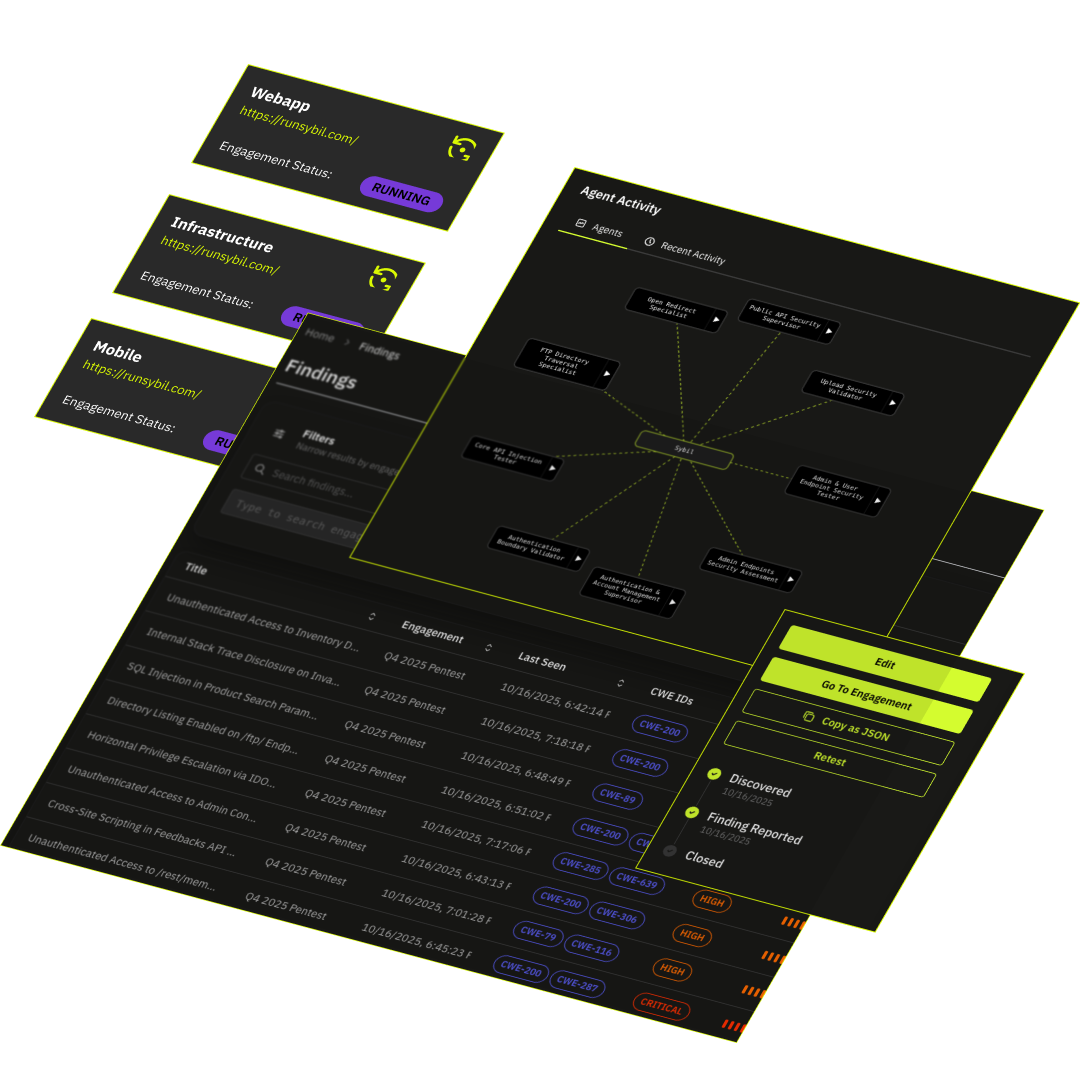
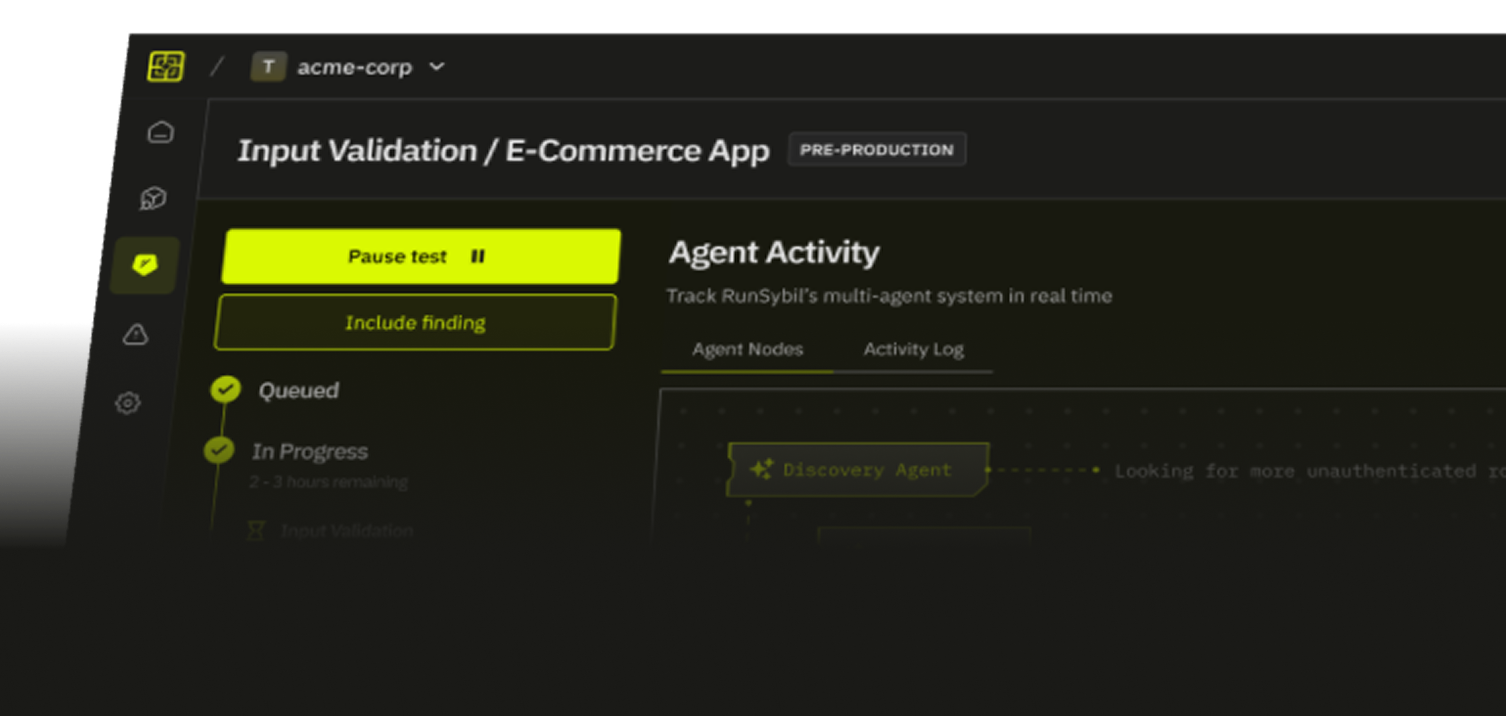
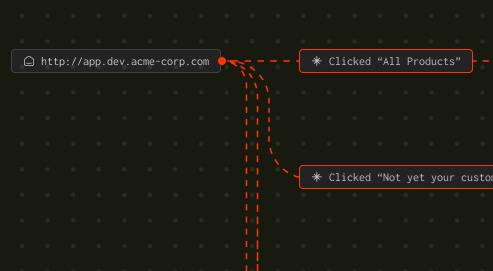
Instead of scaning for signatures, it reasons like an attacker. Sybil chains vulnerabilities across your stack to surface real, exploitable paths. Get only the findings that matter.
Sybil re-evaluates continuously so your security posture reflects your systems as they existright now.
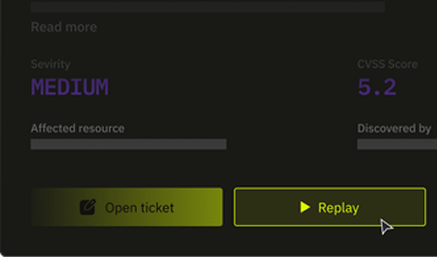
Exploitable findings and quantifiable results
Sybil delivers measurable improvements to your security posture and development velocity, transforming how you approach offensive security

“We wanted a world-class partner for Turbopuffer’s ongoing pentesting needs, and we couldn’t be happier with our relationship with RunSybil. Quick turnaround, attention to detail, and fun to work with—a partner that will grow with us ❤️🔥”

“RunSybil’s expertise was instrumental in enhancing our security posture, providing us with critical insights for a confident launch.”

"RunSybil was an excellent partner for us. They pressure-tested our systems ahead of a major release and delivered fast, high-quality results at a competitive price — on par with top pen-testing firms."
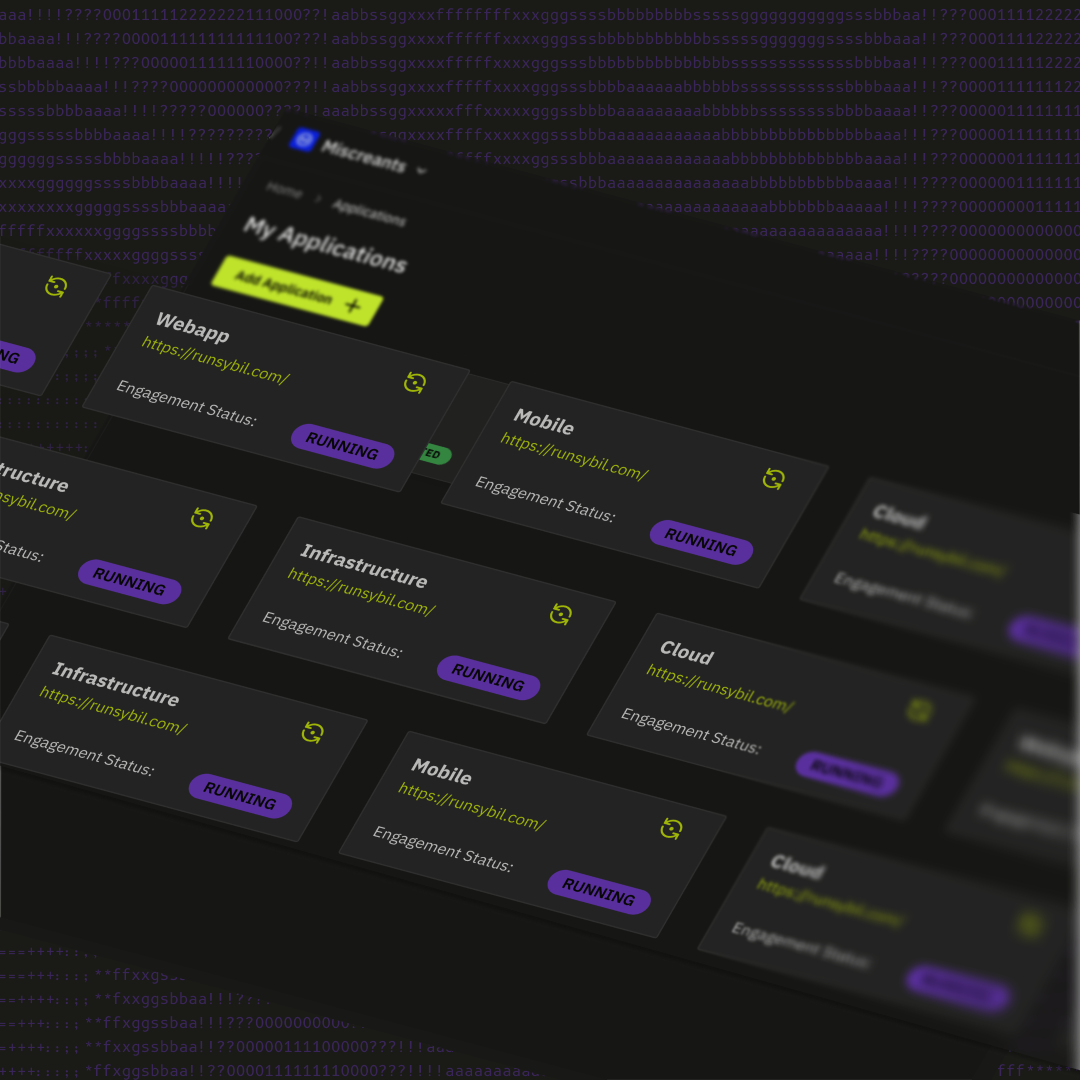
Five ways organizations deploy Sybil
High-Risk Application Security Testing
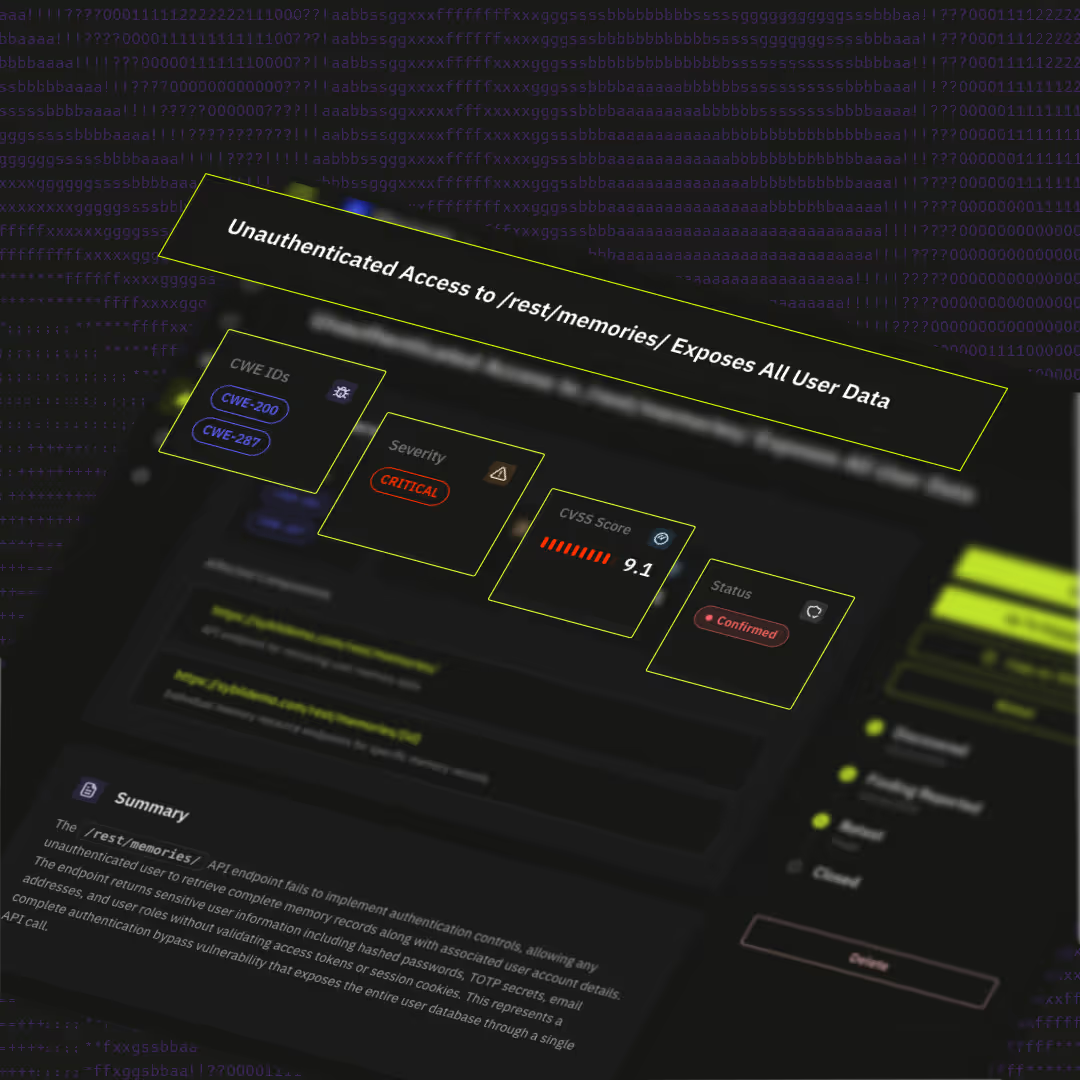
Your critical systems, the ones handling customer data, transactions, and access, need more than a scanner and an annual pentest. Sybil tests them the way an elite researcher would: probing logic, chaining vulnerabilities, and validating exploitability. On every deployment.
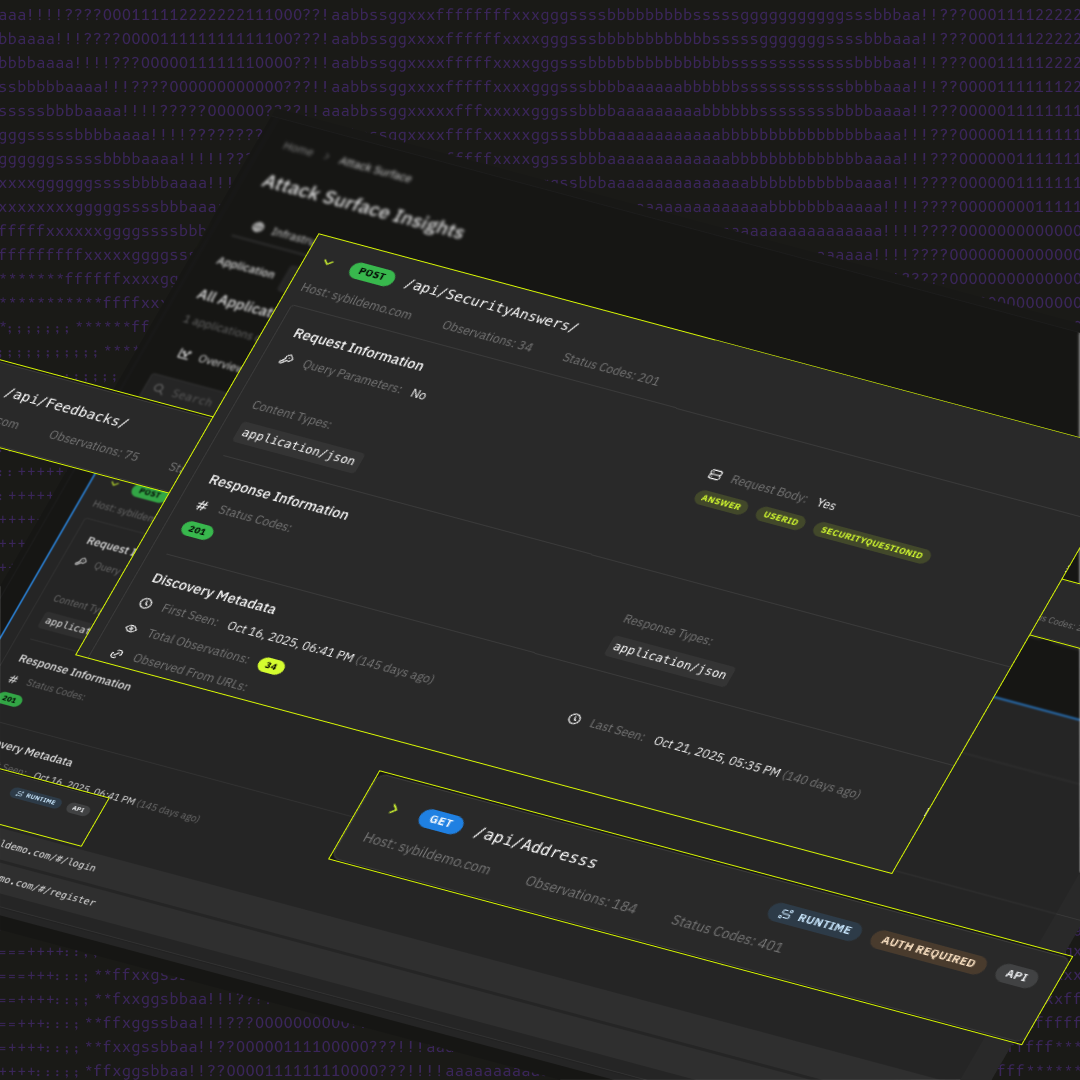
Continuous Attack Surface Monitoring
Sybil builds a model of your application and infrastructure, and keeps it current. On every deployment, it doesn't re-run generic checks. It evaluates what changed, understands how that change affects your specific attack surface, and surfaces only the risks that are new or newly exploitable. Coverage that gets smarter with every sprint, not just faster.
Multi-Tenant & Business Logic Testing
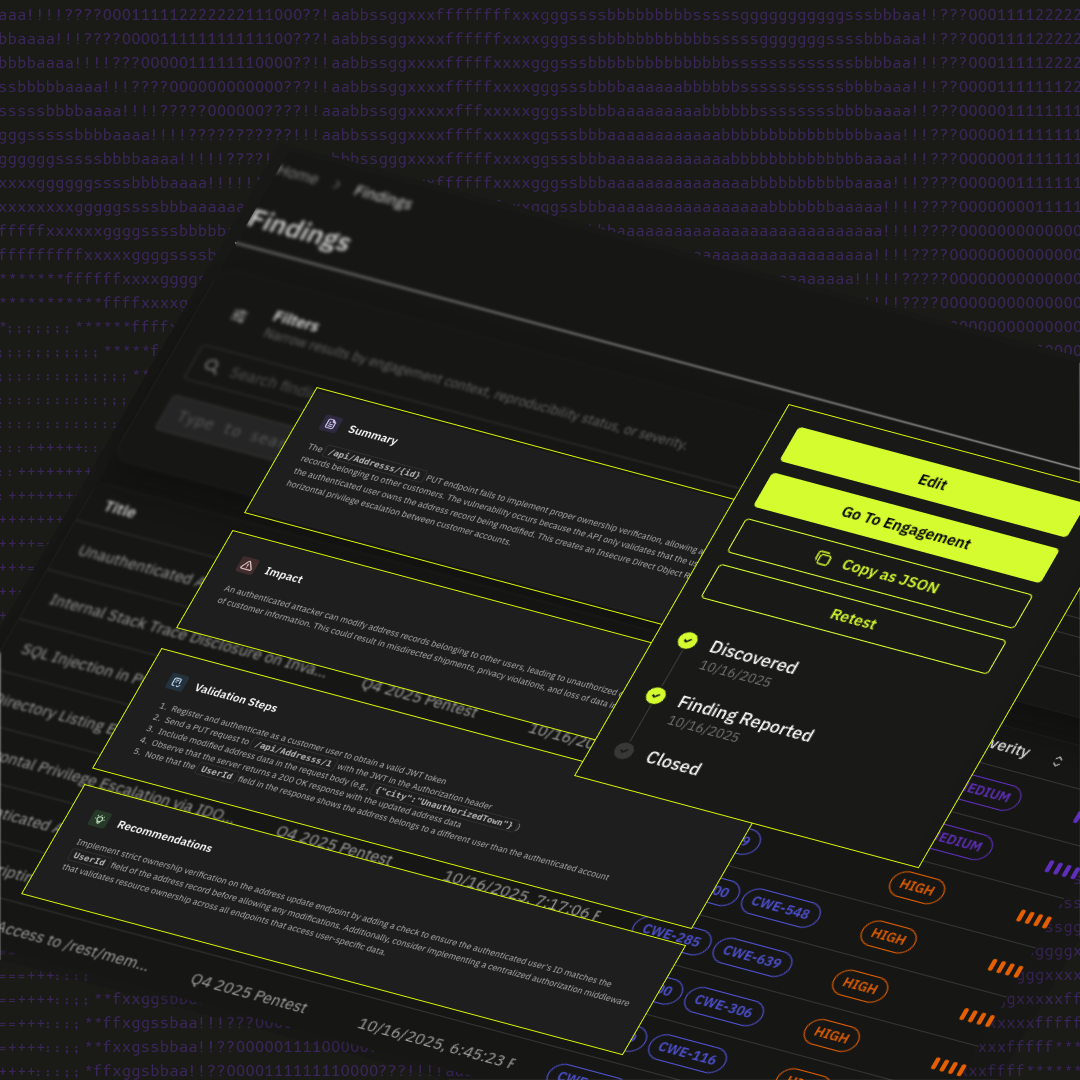
Cross-tenant data access, privilege escalation, transaction manipulation, broken authorization. Sybil tests for these through adversarial reasoning, the same way an attacker would find them, not a scanner.
Bug Bounty & Pentesting
Bug bounties are expensive and unpredictable. Point-in-time pentests go stale the moment you ship. Sybil replaces both with continuous coverage across application and infrastructure layers, pre-validated findings, zero triage burden, predictable cost.
Cloud & Infrastructure Security Validation
IAM misconfigurations, container escapes, CI/CD secret exposure, lateral movement paths. Most tools test these in isolation. Sybil reasons across layers, identifying how an application vulnerability becomes the entry point for full infrastructure compromise. The chains that connect them are where real breaches happen.

Sybil enables CTEM
Most CTEM programs stop at Discovery and Prioritization; finding exposures and ranking them by theoretical risk. RunSybil owns Phase 4: Validation.
Sybil continuously attacks your applications and infrastructure with real adversarial reasoning, proving whether what your other tools found is actually exploitable. Not simulated. Not periodic. Continuous offensive testing that turns your CTEM program from a framework into an operational reality.
Get a sample RunSybil Report